Most people starting a career in IT security have a huge interest in topics like hacking, programming, system administration, networking and so on. When you apply for a junior position, employers normally expect basic skills and huge motivation. In this article you can find some useful resources for learning the basic skills that are useful for all career paths in IT security. More specific articles for specialized career paths like penetration tester, DFIR expert, malware expert and so on, are about to follow.
If you have any ideas or suggestions for additional useful courses, please feel free to leave a reply in the comment section below or just add them to your personal training list.
I suggest to look for suitable courses or certifications, to set yourself a goal and make a plan how to reach your goal.
If you want to read how I started my career in IT security have a look here.
Programming
Depending on your career, you should have knowledge in various programming languages. As a penetration tester, these could be assembly, C, javascript, HTML, python and bash for the beginning. Programming skills are not only useful for penetration testers, but also for other career paths. For example in a blue team, programming skills are very useful for automatization.
In this section you can find some examples for learning basic programming, more specialized examples follow in the career path sections.
HTML
Html & JavaScript
Learn Basics by building your own Computer
Build a Modern Computer from First Principles: From Nand to Tetris
Content: Teaches the basics of computer sience by building a computer from ground up. There is also a great TED talk about the course.
Career: All
Level: Beginner
Price: Free or with certificate
Programming Python
Python might be the most important language to learn as a starter.
Programming for Everybody (Getting Started with Python)
Content: Python Basics
Career: All
Level: Beginner
Price: Free or with certificate
There is a ton of free resources on the web, this also looks useful:
https://www.python.org/about/gettingstarted/
https://www.learnpython.org/
More EDX courses: https://www.edx.org/learn/computer-programming
More coursera courses: https://www.coursera.org/browse/computer-science/software-development
Programming Bash, Learning Linux
For all career paths, you will need Linux skills.
https://www.bash.academy/
https://www.learnshell.org/
http://tldp.org/HOWTO/Bash-Prog-Intro-HOWTO.html
If you lack of basics in Hardware, OS and so on consider this one:
https://www.professormesser.com/free-a-plus-training/220-901/comptia-220-900-course/
Networking
Professor Messer’s CompTIA N10-007 Network+ Course
Content: Great and free video course for preparing the CompTIA Network+ exam, I recommend to add a book nevertheless.
Career: All
Level: Beginner
Price: Videos are free
All in One CompTIA Network+
Author: Mike Meyers
Content: Coverage of the CompTIA Network+ certification exam objectives, goes into the topics in depth. I liked the questions after each chapter. Came with a CD with an exam simulator long ago, now the content is online.
Career: All
Level: Beginner
Buy at Amazon U.S.
Buy at Amazon Germany
You may consider to do the certification for the CV.
More Coursera courses: https://www.coursera.org/browse/computer-science/computer-security-and-networks
Learn about http:
https://developer.mozilla.org/en-US/docs/Web/HTTP
https://www.tutorialspoint.com/http/
Basis Security
The Cuckoo’s Egg Decompiled Course
Content: Highly recommended course by Chris Sanders, teaching the basics of attacking and defending networks through the lens of the famous “The cuckoos Egg” book by Clifford Stoll.
Career: All
Level: Beginner
Price: Free
Professor Messer’s CompTIA SY0-501 Security+ Course
Content: Same as the Network+ course for Security+, I also recommend to read a book additional for preparation.
Career: All
Level: Beginner
Price: Videos are free
Mike Meyers’ CompTIA Security+ Certification Passport
Author: Dawn Dunkerley
Content: For preparing the CompTIA Security+ Certification this book is recommended. It covers every topic from the exam and also includes review questions as well as a practice exam.
Career: All
Level: Beginner
You may consider to do the certification for the CV.
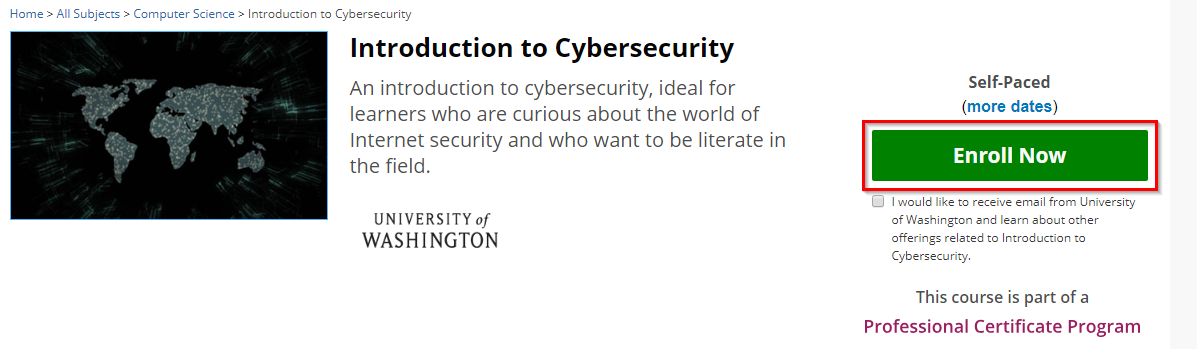
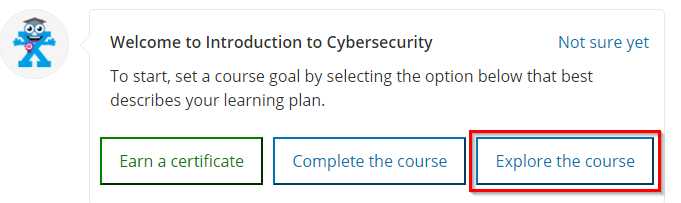
Introducion to Cybersecurity
Content: Short non technical introduction course for everyone who is curious about cybersecurity. Explains the basic concepts from a higher level.
Career: All
Level: Beginner
Price: Free or with certificate
More EDX courses: https://www.edx.org/learn/cybersecurity
More Coursera courses: https://www.coursera.org/browse/computer-science/computer-security-and-networks
Stay tuned, my next article will be about the career path for penetration testers.
Links
- https://www.owasp.org/index.php/Main_Page
- https://www.youtube.com/user/OWASPGLOBAL
- https://www.dfir.training/
- https://www.tutorialspoint.com/
- https://www.reddit.com/r/netsec/
- https://seclists.org/
- https://www.ethicalhacker.net/
- more here: https://welearnsecurity.com/links/
Thanks @SparkyS04 for proofreading.