As a second course (see previous blog post for the first course) I bought “Certified Cyber Threat Intelligence Analyst” which has the same instructor as “Certified Advanced Persistent Threat Analyst”.
Section 1: Phases Overview
The first three videos give an overview on the agenda (hunting, features&behavior extraction, attribution, tracking and take down).
The two videos following about hunting are explaining the goal of hunting, including information gathering from different sources, such as VirusTotal, underground forums, deep web and so on.
Features & Behavior Extraction covers what to extract from malware for further insight in five videos, like metadata, language, metadata, exif, strings, IPs etc..
The videos following are about Clustering and Correlation, Threat Actor Attribution, Tracking and Taking Down, followed by the quiz. Without going too deep, the videos cover sandboxing, dynamic and static malware analysis, malicious events, passive DNS, Graph DB, C2 infrastructure, TTP (yay!), OSINT and more.
The next sections go through each phase with more depth.
Section 2: Hunting
The hunting section starts with two videos with hunting and VirusTotal. This covers different techniques helping hunting, yara rules, retrohunt, searching and research. The three videos about Hacking Forums come with some examples. For this topic I highly recommend to read https://krebsonsecurity.com/?s=hackforums & https://krebsonsecurity.com/tag/darkode/ and so on for more in depth information.
The two Deep Web parts are also pretty basic, nothing new if you are in cyber for some time. Also, I do not like it when “Deep/Dark Web” is only refered to shady or criminal activities. The next video is about Honeypot & OSINT, especially honeypots are big fun and you should setting up one.
The two lab videos are much longer than the other ones (<30min), and seem to be taken from a different course. The first is about VirusTotal Intelligence which gives a nice introduction to hunts, retrohunting, clustering and other functions of the platform. The second lab video is about yara. It is being said that you can get access to VT from the trainers, but I got no answer to my request, which is kind of disappointing.
Section 3: Features Extraction
The first two videos are a short introduction to the topic “Features Extraction Goal”, which is more like an introduction to static malware analysis.
The next two videos cover “Import Table Hash (imphash)”. I always have a bad feeling when people talk about MD5 in this area, since collisions are possible with MD5. Further some of the statements are a bit dangerous, for example “Cannot revert the hash to get original content” only applies for content with a certain size that is not available in any form. When you have a hash and find a matching file, for example in a antivirus database like virustotal you totally can get the original content. Just imagine a scenario where an analyst from company A is giving a bunch of MD5 to an external company B. When an employee of company A ever uploaded internal documents to VT, company B now can assign the MD5 to the uploaded document. This is why you do not share all your indicators folks.
The instructor is even talking about that hashes are “security protection features”. Pentesters love finding MD5 hashes of passwords, nothing cracks better ;).
So depending on the usecase please consider using stronger hash algorithms, also in malware analysis. Imphash might be OK at this place though, since it only refers to the import table and not to the whole binary.
For better understanding: https://www.fireeye.com/blog/threat-research/2014/01/tracking-malware-import-hashing.html.
“Just because two binaries have the same imphash value does not mean they belong to the same threat group, or even that they are part of the same malware family”. In the course it is being said that similar imphashes mean that the malware has more or less the same source code, which is unfortunate and false leading.
The following video is about “Fuzz Hash (ssdeep)”, refer the link list for further explanation.
The first lab video is “Extracting VBA Macros with Didier Stevens Tools”. If you ever have the chance of catching up Didier Stevens and one of his workshops at a conference go there, from all I heard it is awesome and I look forward to it. First the video is going into more features of VirusTotal, then going to emldump and oledump. The second lab video is about C2 IP Pivoting, which refers to finding IPs in VBA macros in this case.
The section ends of course with a quiz.
Section 4: Behavior Extraction
Eight short videos about dynamic analysis including “Dynamic Indicators”, “Process Infector and Keylogger”, “Passive DNS” and the quiz. I won’t go deep into it here, since the titles are pretty self explaning and mainly cuckoo output is used here. Play for yourself with that ;).
Section 5: Clustering & Correlation
The first four videos are about “How Clustering & Correlation Works”. Here some of the classifiers are explained with examples and what it is for. Two videos about GraphDB follow, and a longer lab video & of course the quiz. Interesting that the tutor is not refering to the product, but to a category (neo4j, maltego) when talking about GraphDB, which was a bit confusing first.
The lab video looked good and interesting, hope I will have some time in the future to play with the VT features. The video contains an intro to viper (awesome tool) and how to use viper for correlation.
Section 6: Attribution
The topics in this section are “Where are they located?”, “Who are the targets”, “Initial Compromise”, “Privilege Escalation”, “Persistance”, “Lateral Movement”, “Exfiltration Strategy”, “Profiling the Attacker” and the final quiz. Some parts are pretty similar to the APT course.
For the discussion about attribution, in my thinking it is an approach for getting useful information for fighting an attacker. If it works, great. On a higher level things might be a bit different and give much opportunity for open discussions ;).
Section 7: Tracking
In the tracking section the videos are about “Passive DNS & Internet Port Scan”, “Lookups, OSINT and Hacking Forums” as well as the quiz. The section is pretty short and goes only a bit more in depth as section 1.
Section 8: Taking Down
This is covering “Sinkhole”, “How it works?”, “Hacking Forums”, “Victim Notification” & the quiz, the section is also short as the two sections before. Of course this is simplified, be careful, a lot can go wrong here.
Conclusion
As in the APT course, the course is OK for beginners, but please have in mind that some content is not high qualitiy and not complete, which is hard. Therefore I give this course three stars out of five.
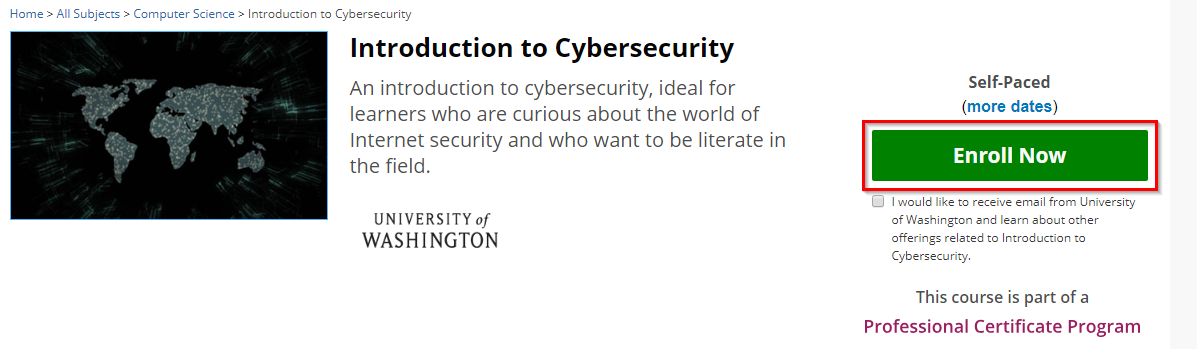
I can also recommend “Malicious Software and its Underground Economy: Two Sides to Every Story” (https://www.coursera.org/learn/malsoftware), if still possible, which I took some time ago, the author of this course actually took down a C2 infrastructure and it is pretty interesting.
Links, as in the previous artice I added some links that are not originaly from the course:
https://www.udemy.com/cybersecurity-threat-intelligence-researcher/
https://www.heise.de/security/artikel/Threat-Intelligence-IT-Sicherheit-zum-Selbermachen-3453595.html
https://en.wikipedia.org/wiki/Cyber_threat_intelligence
Russian financial cybercrime: how it works
Click to access wp-cybercrime-and-the-deep-web.pdf
http://www.scmp.com/tech/innovation/article/1840925/chinese-forums-offer-hacking-courses-around-us100-cyber-attacks
https://cuckoosandbox.org/
http://graphdb.ontotext.com/
https://www.virustotal.com/
https://virusshare.com/
https://krebsonsecurity.com/
Click to access The_Diamond_Model_for_Intrusion_Analysis_A_Primer_Andy_Pendergast.pdf
https://govolution.wordpress.com/2016/10/24/the-first-15-days-of-a-password-honeypot/
https://github.com/govolution/betterdefaultpasslist
https://en.wikipedia.org/wiki/Maltego
https://github.com/laramies/metagoofil
https://virustotal.github.io/yara/
https://remnux.org/
https://github.com/govolution/avet
https://www.mscs.dal.ca/~selinger/md5collision/
Meaningful MD5 Collisions: Creating executables
https://www.fireeye.com/blog/threat-research/2014/01/tracking-malware-import-hashing.html
http://blog.virustotal.com/2014/02/virustotal-imphash.html
https://ssdeep-project.github.io/ssdeep/index.html
Release: emldump.py Version 0.0.3
oledump.py
https://malwr.com/
Click to access first2005-paper.pdf
https://viper.li/
View at Medium.com
https://en.wikipedia.org/wiki/DarkComet