This article is not for learning quantum computing (I am not the right person for that), but to understand some of the implications for IT security and maybe give some help in taking the very first steps.
Introduction to Quantum Computing for Dummies
Since it is so popular let us ask ChatGPT:
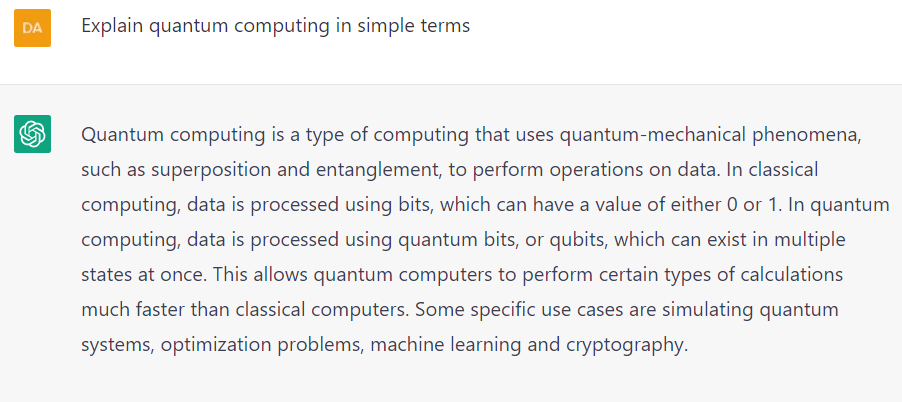
OK, know that it is all clear, let’s move on!
I watched these as an easy to understand introduction into this complex topic.
Quantum Computers Explained in a Way Anyone Can Understand
Dig deeper into Quantum computing
If you want to dig deeper have a look at this article, which also links some free introducing books:
https://builtin.com/software-engineering-perspectives/how-to-learn-quantum-computing
This also looks interesting:
Braking RSA
A current discussion is when/how RSA will be broke.
RSA’s demise from quantum attacks is very much exaggerated, expert says
Expert says the focus on quantum attacks may distract us from more immediate threats.
One more article about this topic:
Fujitsu: Quantum computers no threat to encryption just yet comment bubble on black
Heavily hyped tech bound for some sort of milestone by decade end
https://www.theregister.com/2023/01/24/fujitsu_quantum_encryption/
Implications in depth
And if you want to dig deeper in these topics here are three fantastic resources:
Quantum computers are nuclear weapons of the tech – but their potential is immeasurable
As scientists across the world express their excitement about the development of quantum technology, others are worried about the dangers it poses to today’s encryption and the potential benefits it could offer to cybercriminals.
https://cybernews.com/crypto/quantum-computers-promises/
Ensure to watch the video at the end:
The Story of Shor’s Algorithm, Straight From the Source | Peter Shor
How Quantum Computers Break Encryption | Shor’s Algorithm Explained
Conclusion
For me it is hard to look into the future here, this field is much too complex and I have only some basic understanding. From what I see at the current point there is no direct impact and we all should be aware that there is also some hype. Maybe you should start to consider what might happen if your current encryption will be broke in the future. I hope I showed a path for starting research for everyone who is interested.
Quantum Computing can have great impact on lot’s of fields, obviously IT security and encryption is only a very small fraction of it. I wonder what it will mean for all STEM fields like astronomy, material research, medicine, understanding the brain, the universe and all the rest.