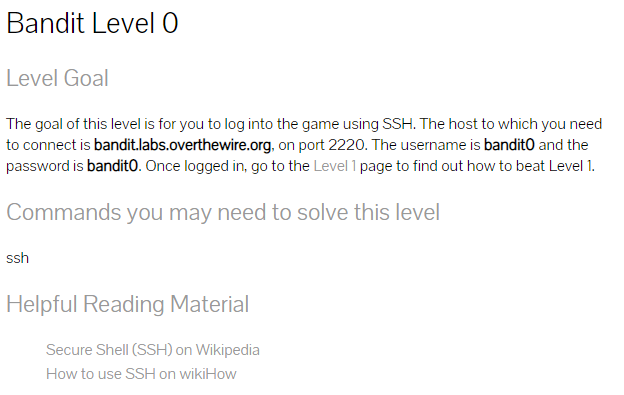
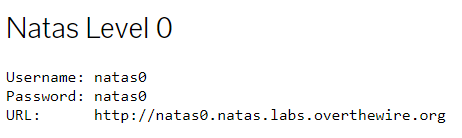
Security Researchers work in the field of bug bounties and exploitation, often they are independent but sometimes they also work as employees. I think that both paths are not easy, but of course it can be done. On both paths you can earn lots of $$$ but I also heard of people who came out disappointed. Some people starting this as a side job and then go independent. If you don’t know some basics look here and here.
The reason why I put both paths in one post is that for me you need a similar mindset. You have to be highly motivated, need to learn a lot before you gain some success (well, at least for most people) and if you go independent you work on your own. For both you need a plan or tactics, you can’t just start hacking and hope to find something.
When you want to participate in bug bounties normally you are using platforms like hackerone or bugcrowd, but lot’s of companies have their own bounty programs. Since most of these programs are public this makes starting easy.
On the other hand, when you want to start as a researcher and do exploit development, you also have some public resources like ZDI or zerodium. But what is more important than in bug bounty, is networking with other researchers and companies. One way is to go at conferences and trainings, have a look at the links section of this article.
Both paths might take months or even years until you get into it, so this article can only be a starting point that I hope is helpful.
Links
Bug Bounty
Blog Articles, programs
- https://renaudmarti.net/posts/first-bug-bounty-submission/
- https://blog.usejournal.com/bug-hunting-methodology-part-1-91295b2d2066
- https://gowsundar.gitbook.io/book-of-bugbounty-tips/
- https://medium.com/bugbountyhunting
- https://github.com/jhaddix/tbhm
- https://codingjames.ca/learning-bug-bounty-hunting/
- https://www.tripwire.com/state-of-security/security-data-protection/cyber-security/essential-bug-bounty-programs/
- https://www.guru99.com/bug-bounty-programs.html
LevelUp 0x02 – Bug Bounty Hunter Methodology v3
Advanced Web Attacks and Exploitation (AWAE)
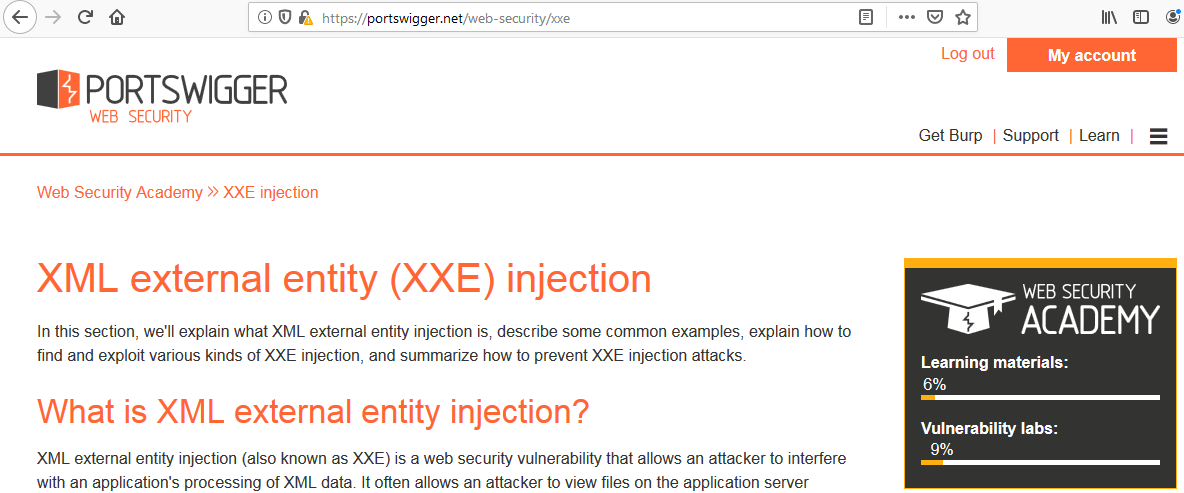
Probably interesting for both paths, but web hacking is more bug bounty for me…
https://www.offensive-security.com/information-security-training/advanced-web-attack-and-exploitation/
Exploiting
35C3 – From Zero to Zero Day
The Exploit tutorials from corelan
https://www.corelan.be/index.php/articles/
That said, I can highly recommend the trainings that you can book at several conferences:
https://www.corelan-training.com/
OSCE- Cracking the Perimeter (CTP)
Also mentioned here before, the Offensive Security course and certification:
https://www.offensive-security.com/information-security-training/cracking-the-perimeter/
OSEE – Advanced Windows Exploitation (AWE)
I also heard great things about the AWE (OSEE) for more in depth exploitation, but I don’t have personal experience here.
Even more links:
https://www.zerodayinitiative.com/
https://zerodium.com/
https://googleprojectzero.blogspot.com/
and especially this article from project zero:
https://googleprojectzero.blogspot.com/p/working-at-project-zero.html
Conferences
As said before, learning new things and networking is really important, so here are some conferences that seem good, you should also consider to take some trainings:
- https://www.offensivecon.org/
- http://zer0con.org/
- https://nullcon.net/website/
- https://infiltratecon.com/
- https://typhooncon.com/
- https://cansecwest.com/
- https://www.blackhat.com/
- https://www.defcon.org/
Books
Hands-On Bug Hunting for Penetration Testers
Author: Joseph Marshall
Content: Go through common bugs in Webapps and introduction to bug bounties
Career: Penetration Tester, Bug Bounty
Level: Beginner
The Shellcoder’s Handbook
Authors: Chris Anley, John Heasman, Felix “FX” Lindner, Gerardo Richarte
Content: Exploiting security holes for Windows, Solaris, MacOSX, Cisco. Although from 2007 still worth reading.
Career: Penetration Tester, Exploiter
Level: Intermediate, Experts
Hacking: The Art of Exploitation
Author: Jon Erickson
Content: Goes from the first steps in Bash and C to in depth exploitation and debugging on Linux.
Career: Penetration Tester, Exploit Developer
Level: Beginner, Intermediate, Expert
And here is a great free book:
Modern Windows Exploit Development
http://docs.alexomar.com/biblioteca/Modern%20Windows%20Exploit%20Development.pdf